Before installation
Introduction
Before you start the installation, we recommend that you go through this checklist to verify that your infrastructure meets our minimum requirements and is configured correctly.
It is possible to host multiple services on the same machine (for security reasons we recommend hosting each service on a separate server).
For example: If Relution and the reverse proxy nginx are installed on the same machine, the server running Relution and the server running nginx refer to the same physical machine. In this case, the server must meet the requirements of both services.
Hardware
The server running Relution has the following minimum requirements →.
Operating System
The server on which Relution is running uses a recommended operating system → and the version of the operating system meets or exceeds the minimum supported version.
Database
The server running Relution has network access to a supported database → server.
This guide contains instructions on how to install MariaDB if you need to install a new database server.
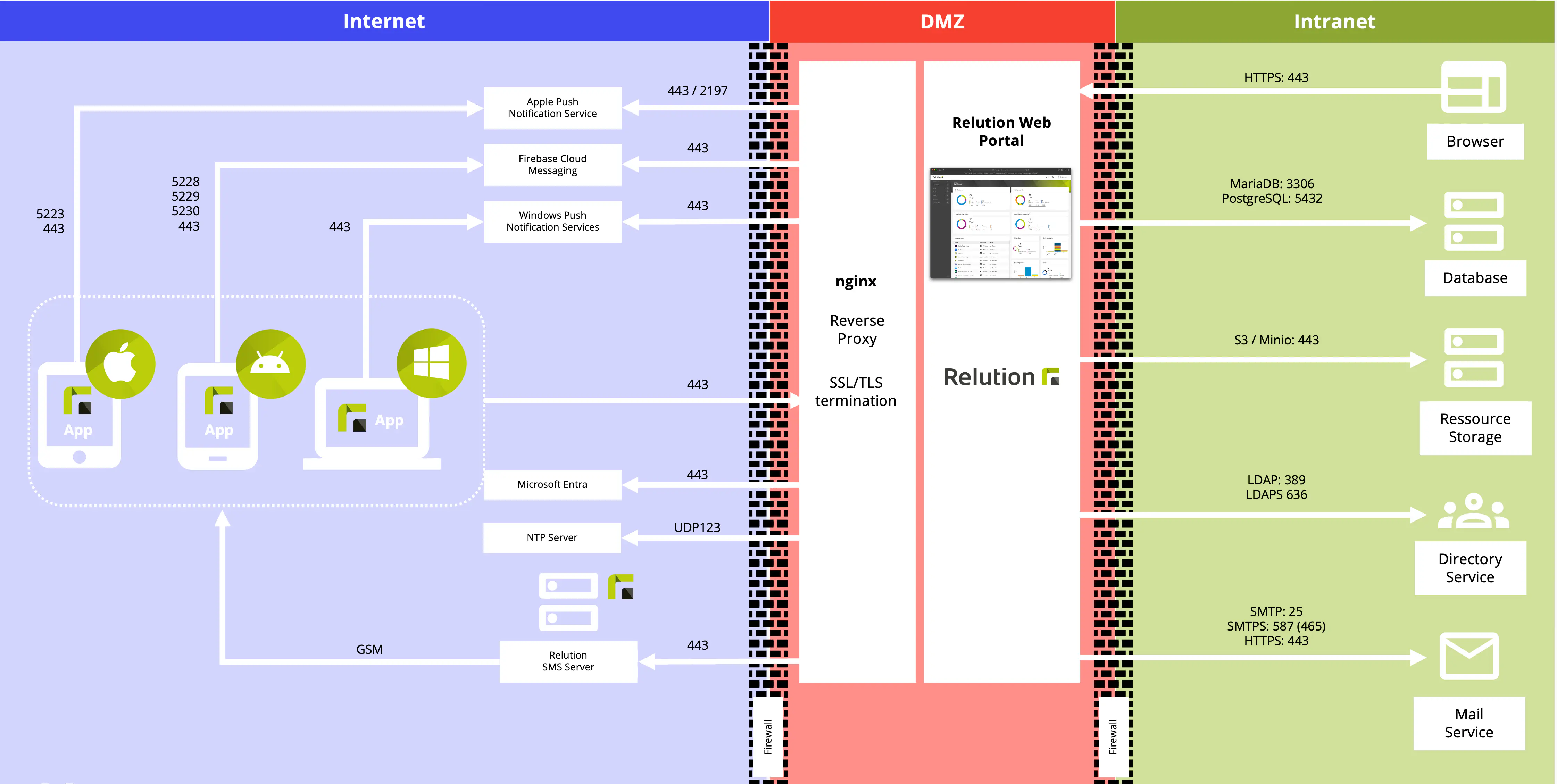
Network infrastructure
The server running the reverse proxy nginx is set up to host a service available on the Internet.
It has a public IP address and a public DNS name or example mdm.example.com. When services are hosted on multiple internal servers, they can resolve each other’s hostnames.
The public IP address must be static. Dynamic IP addresses are not supported. Exceptions: The server is hosted by a cloud provider, such as Amazon Web Services (AWS) or Microsoft Azure, which provide the necessary DNS infrastructure.
Requirement
- Server has direct access to the Internet
- Server has a static IP address
- Server has a public DNS name
- Internal DNS is properly configured and functioning
Firewall configuration
Your firewall is set up to accept incoming HTTP(S) requests from mobile devices and web browsers.
Request
- The reverse proxy is accessible from the Internet via HTTP (80)
- The reverse proxy is reachable from the Internet via HTTPS (443)
- Relution can connect to the Internet (80, 443, 5223, 123 UDP)
- Relution can connect to the SMTP server
- Relution can connect to the database server.
Optional: - Relution can connect to LDAP via port 389 or 636.
Certificates
HTTPS requires a valid SSL certificate from a trusted certificate authority (CA).
- Self-signed certificates do not work, because mobile devices do not trust them by default
- Certificates from Let’s Encrypt → work and are free
You can use W3Techs →. There you will find a list of known certificate authorities based on market share and usage.
| Request | .Fulfilled |
|---|---|
You have a valid SSL certificate and key | .
Relution is shipped with a valid APNS certificate that is used. In this case, the certificate will also be updated with the update of Relution. Automatic updating for own used APNS certificates is not available and has to be organized separately.