OIDC
On this page
Introduction
OpenID Connect OIDC is an identity protocol built on top of OAuth 2.0 that enables secure authentication and authorization for web and mobile applications. It allows users to log in securely to various services while enabling service providers to access verified identity information.
This guide describes how to configure OpenID Connect in Relution using Microsoft Azure as the identity provider.
Settings in Relution
OIDC can be configured in the Relution portal under Settings > OpenID Connect.
The following screenshots include a working configuration example with Microsoft Azure.
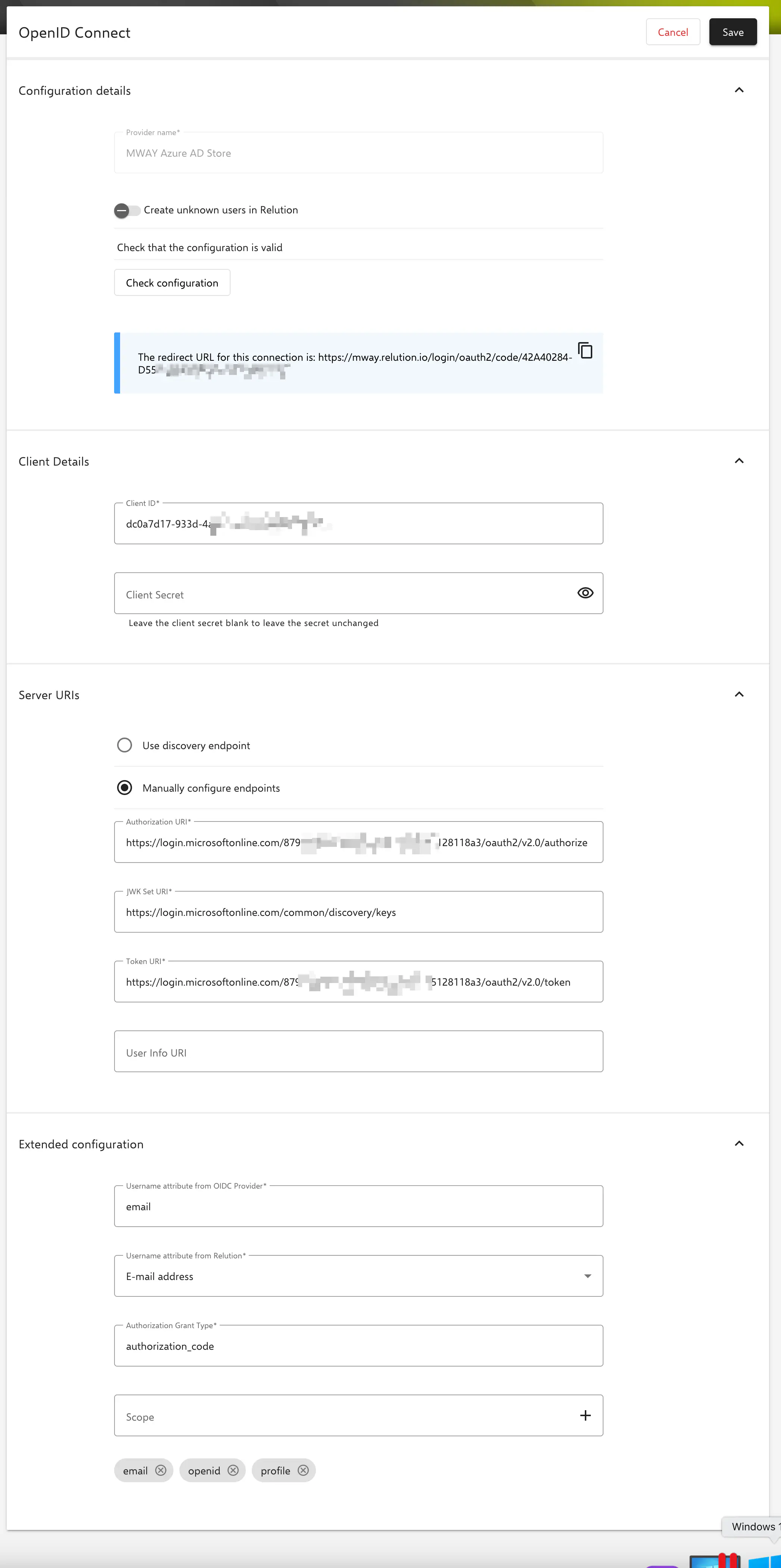
Configuration details
Name of the provider: Displayed as the label on the login button in the Relution portal.
Create unknown users in Relution: Relution creates new users automatically upon successful login with valid OIDC credentials.
If a login is done with an unknown user on the store organization with OIDC configured, it will be created in the store organization. In the case of multiple clients with OIDC configuration, the login must be made via the organization URL so that the unknown user is created in the corresponding organization. This URL is displayed in the portal in the OIDC connections.
Client Details
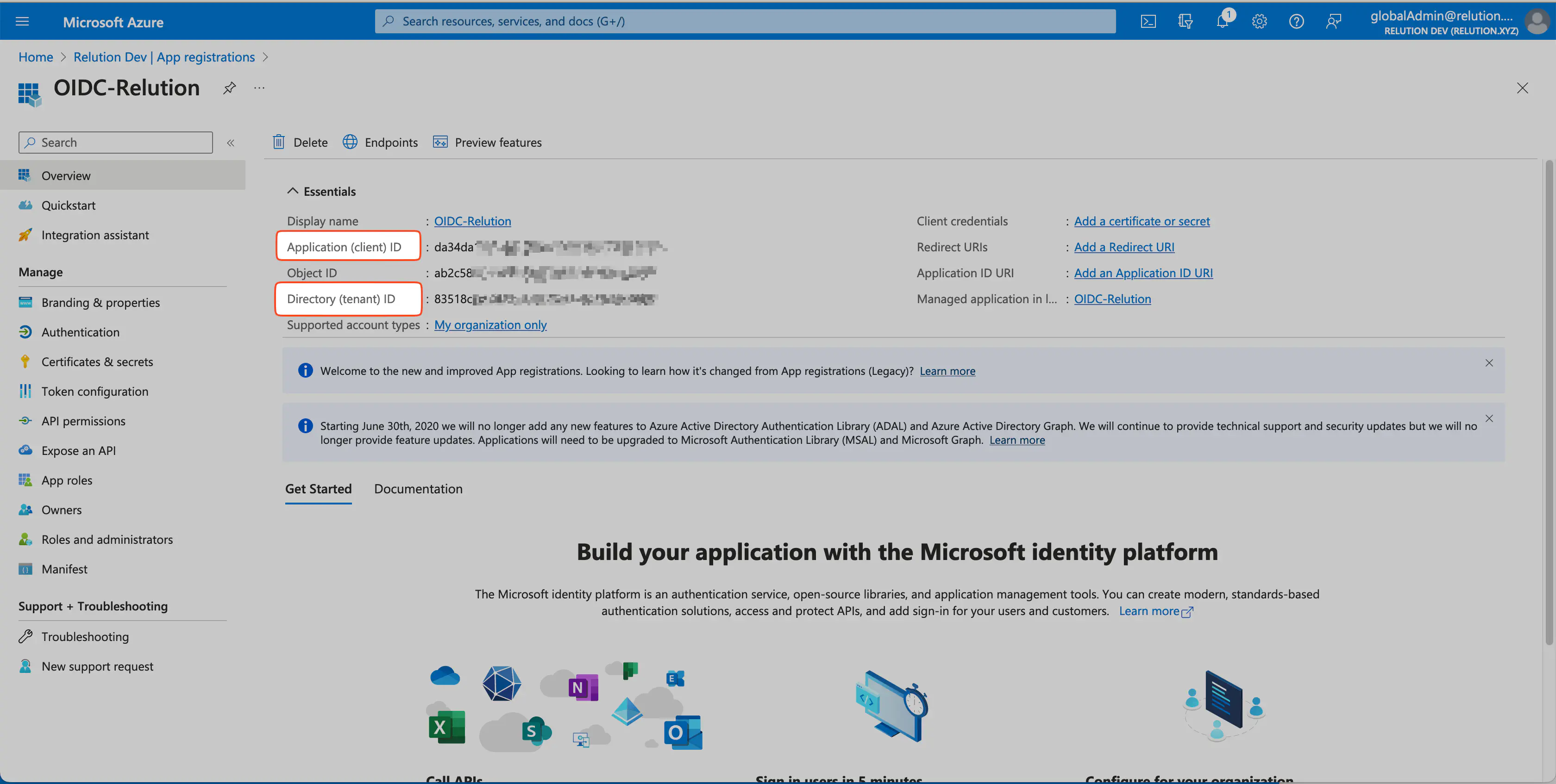
Client ID: Corresponds to the application ID in Azure.
Client Secret: Corresponds to the client secret key to the application ID in Azure.
Server URIs
Use Discovery Endpoint: If supported by the provider, an automatic configuration of the required URIs is performed.
Manual configuration of endpoints: Necessary as soon as automatic discovery does not work.
If using Microsoft Azure, endpoints must be entered manually.
Authorization URI:
https://login.microsoftonline.com/$-your-client-ID/oauth2/v2.0/authorizeJWK Set URI:
https://login.microsoftonline.com/$-your-client-ID/discovery/v2.0/keysToken URI:
https://login.microsoftonline.com/$-your-client-ID/oauth2/v2.0/tokenUser Info URI:
https://graph.microsoft.com/oidc/userinfo
Advanced configuration
The username attribute from the OIDC provider: Specifies the attribute that contains the unique user ID from the identity provider.
The username attribute in Relution: Contains the unique username of the authenticated user.
Authorization Grant Type: The Authorization Grant Type is an OAuth mechanism that specifies how an application obtains access permissions from a user.
Scope: Scopes specifies the identity information or resources the application can request from the OIDC provider.
Settings in Azure
Creating a new app registration
- Logging in in Azure Portal, continuing on
Azure Active Directory.
- Creating new
App registry > Create new registryfor OIDC.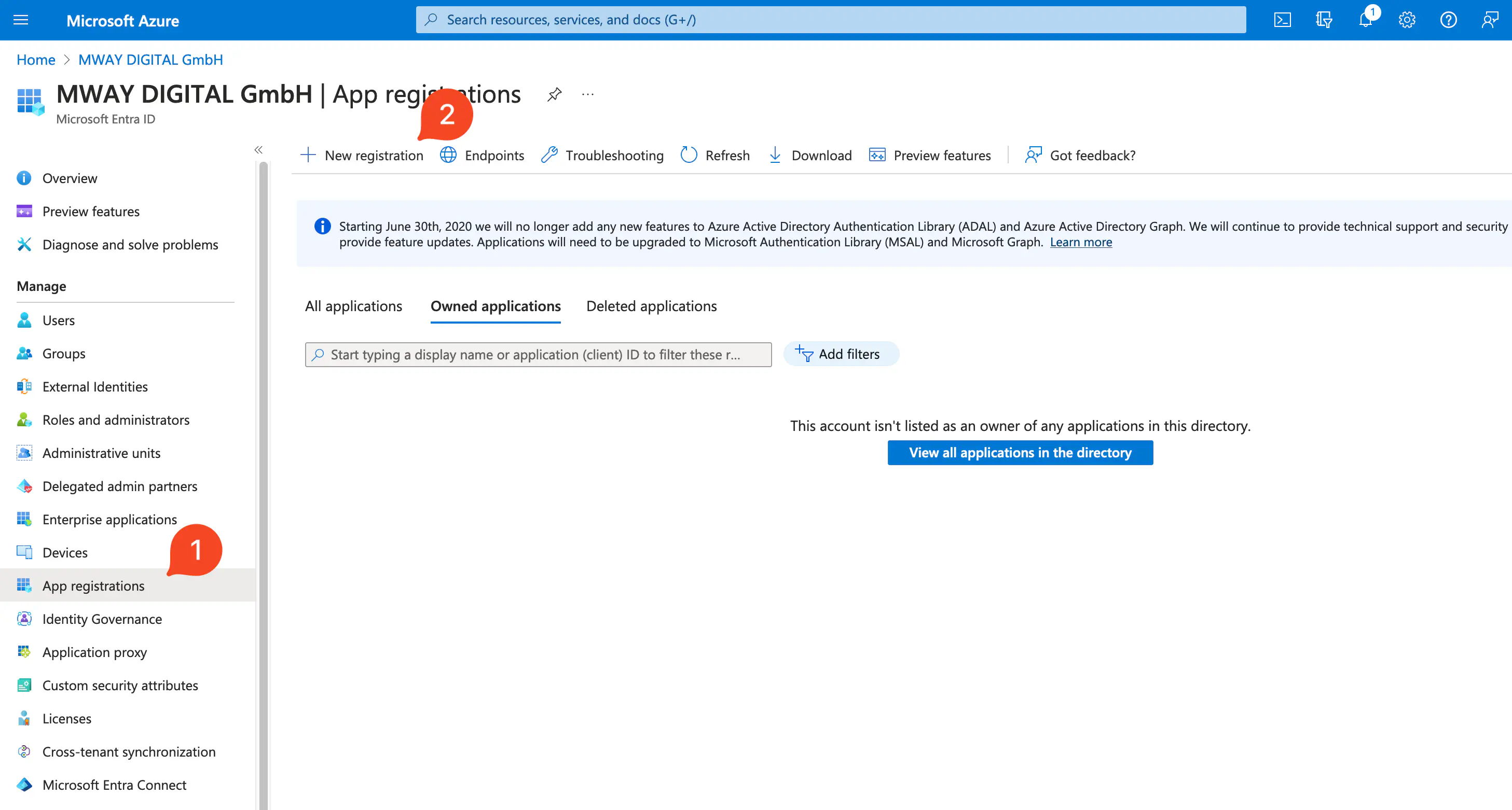
- Provide a name, select account type
Only accounts in this organization directoryand register it.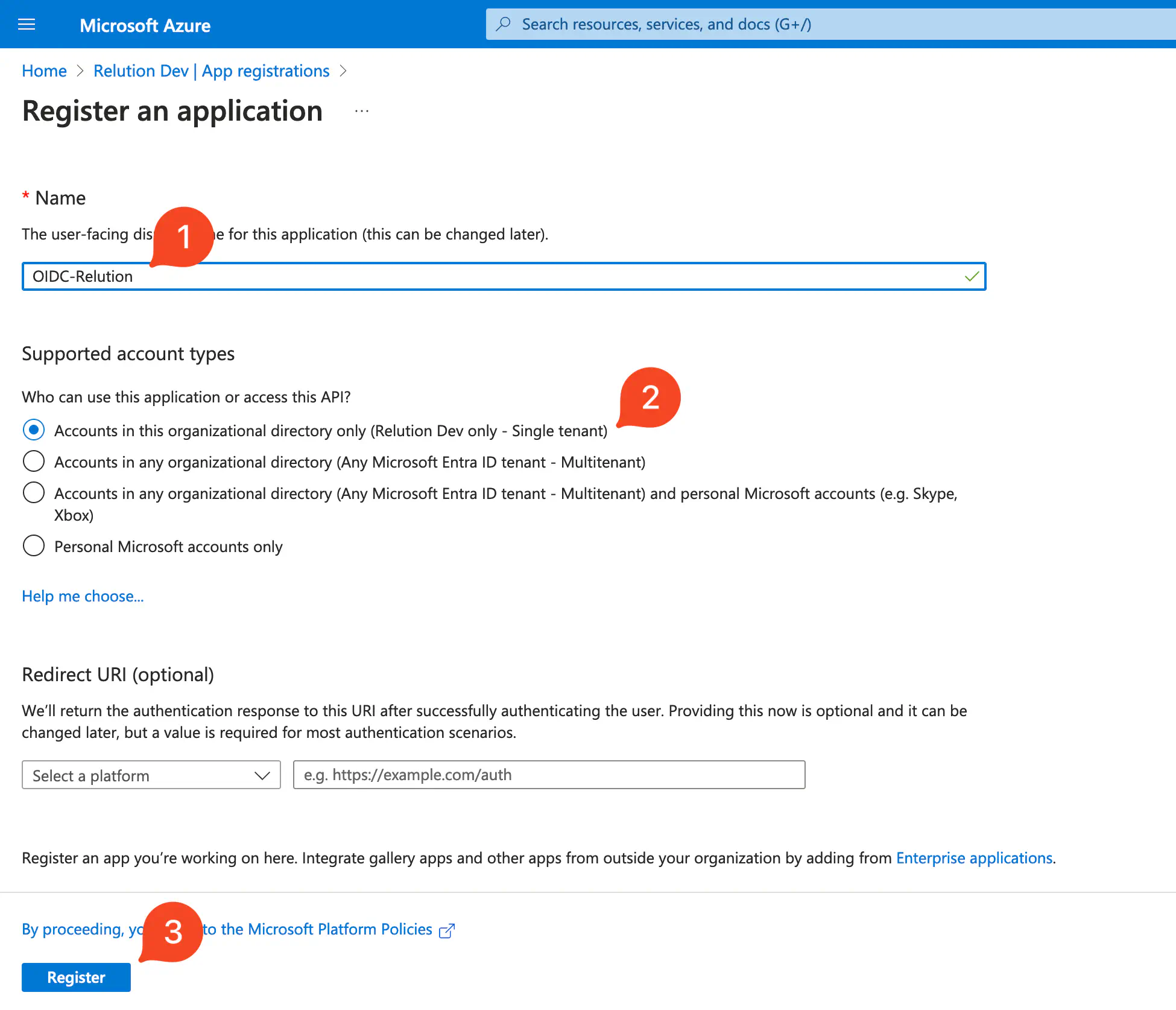
Adding secret client key (Client Secret) under Certificates & Secrets
- The required client secret is created under
Add a certificate or secret.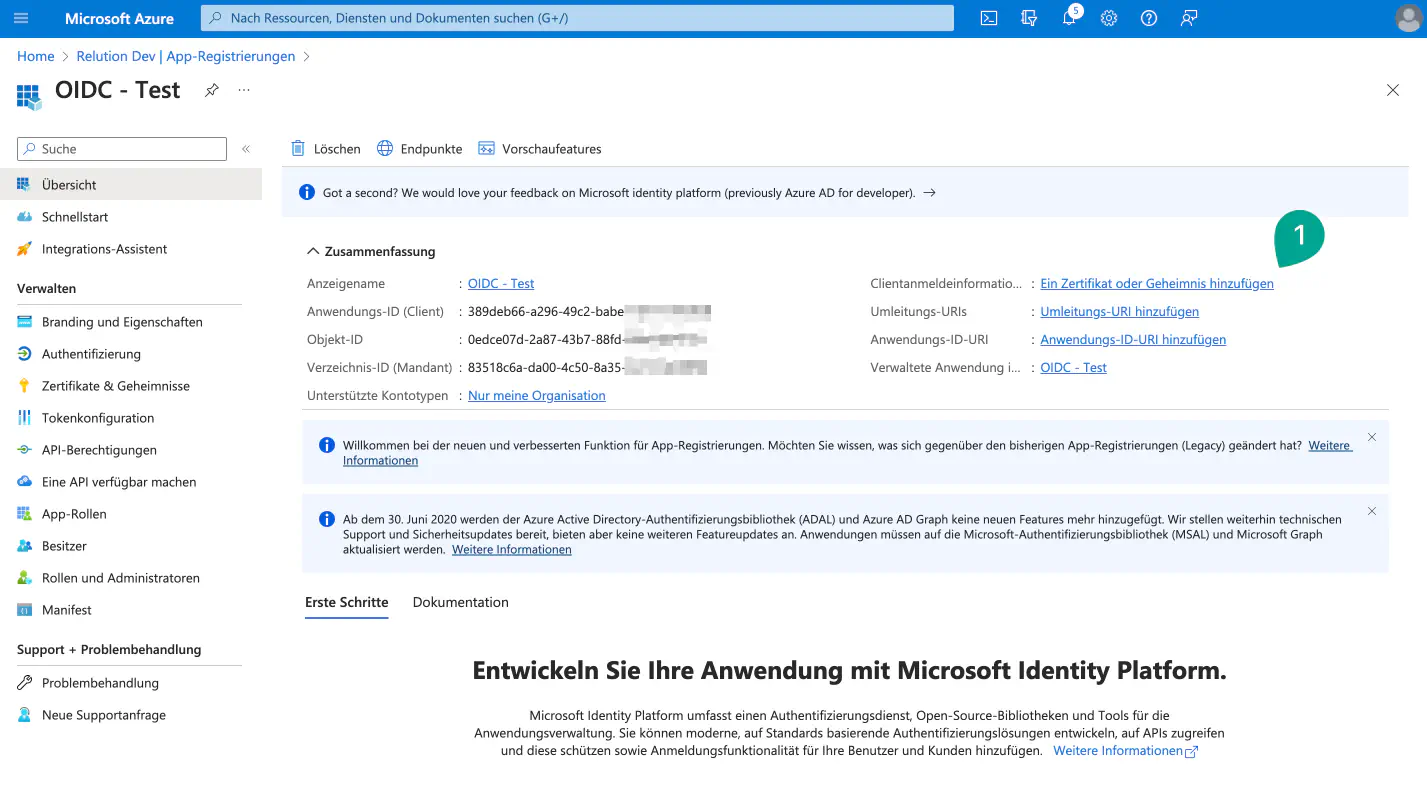
- Via
New secret client keytheDescriptionand validity periodValid untilcan be set.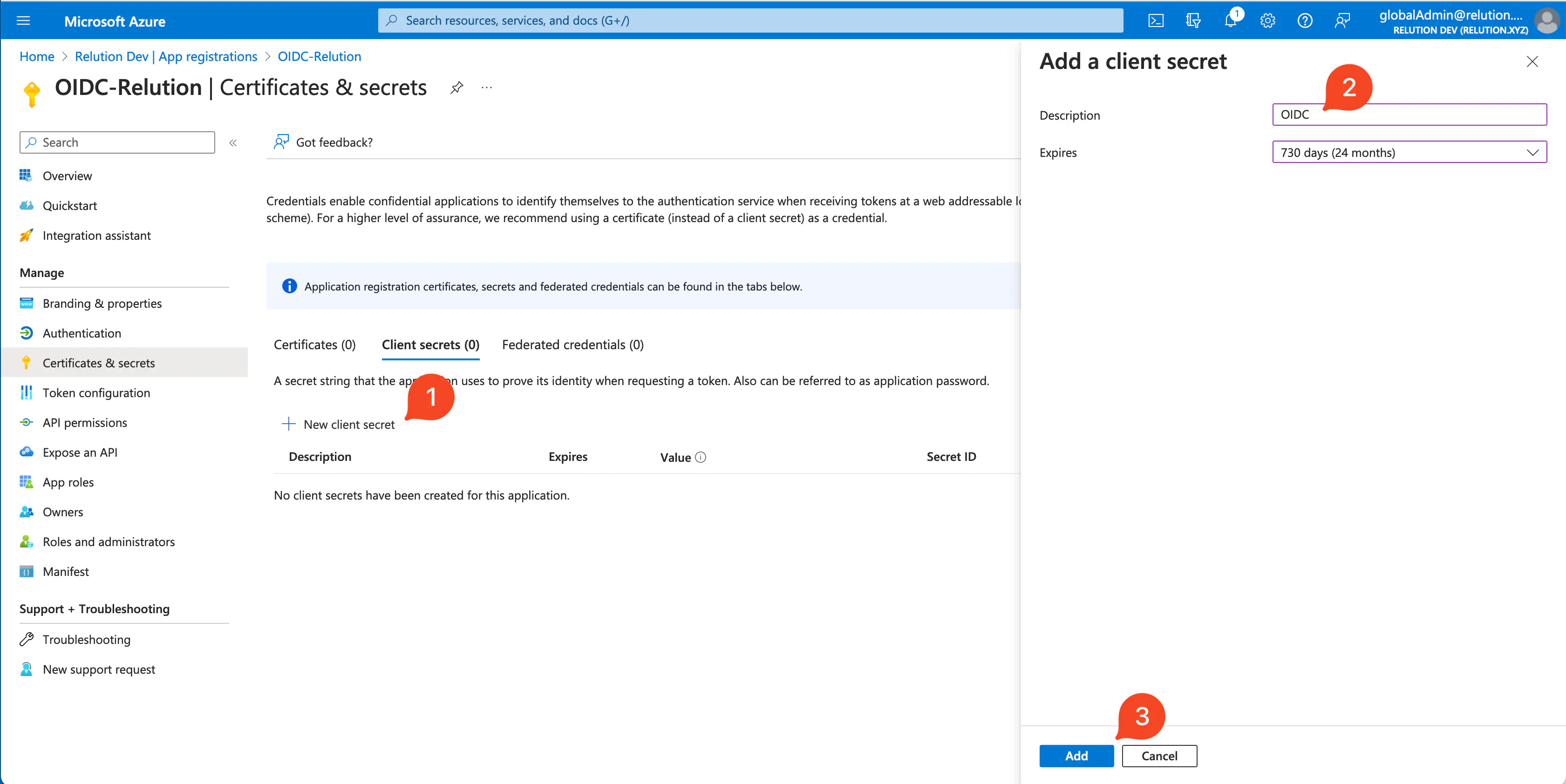
- The client key can be copied directly.
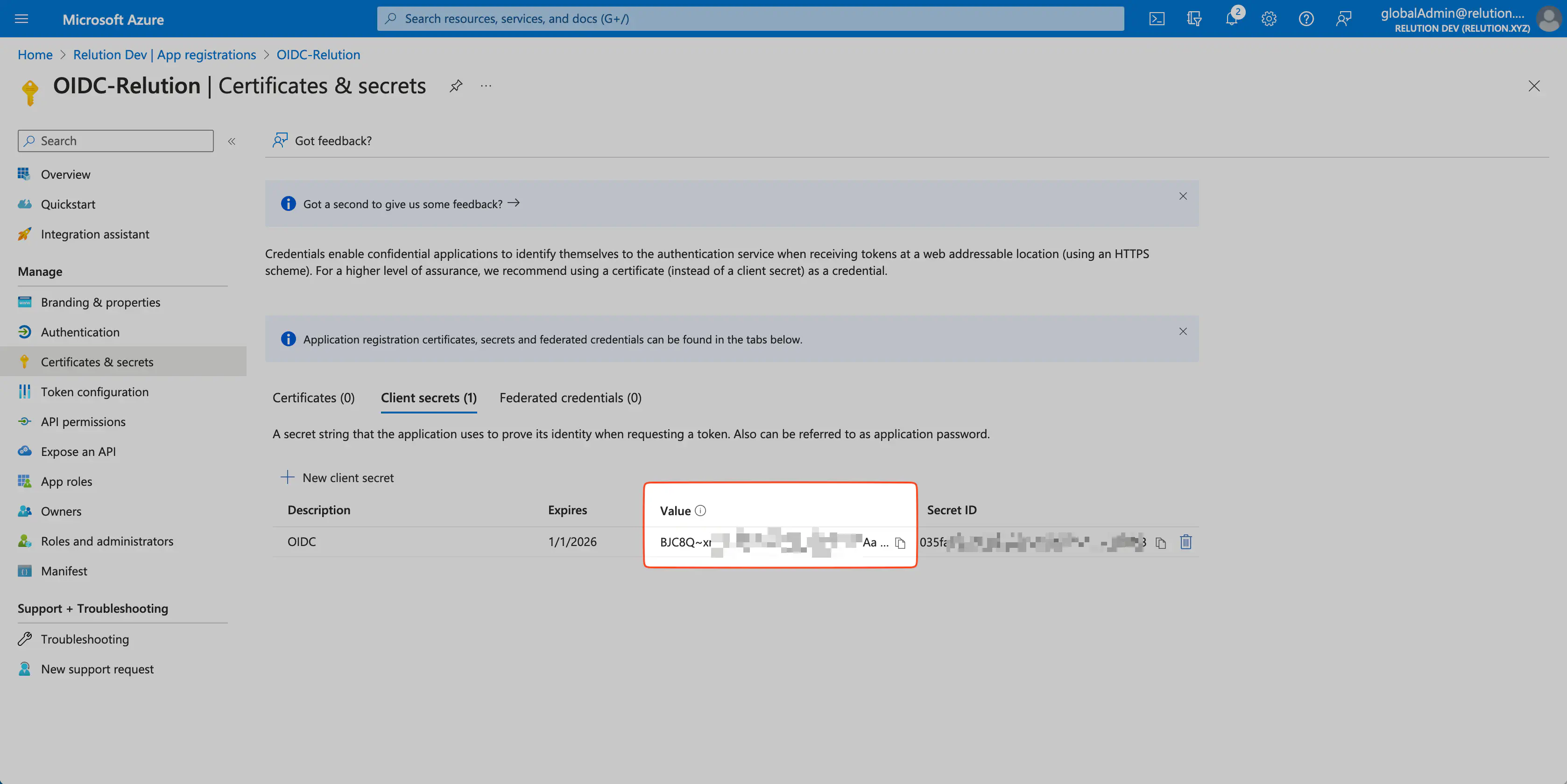
Important: The client key is hown only once after creation. If it expires, Relution will no longer be able to connect to Azure. In this case, a new
secret client keymust be created for the application in Azure and re-transmitted to Relution.
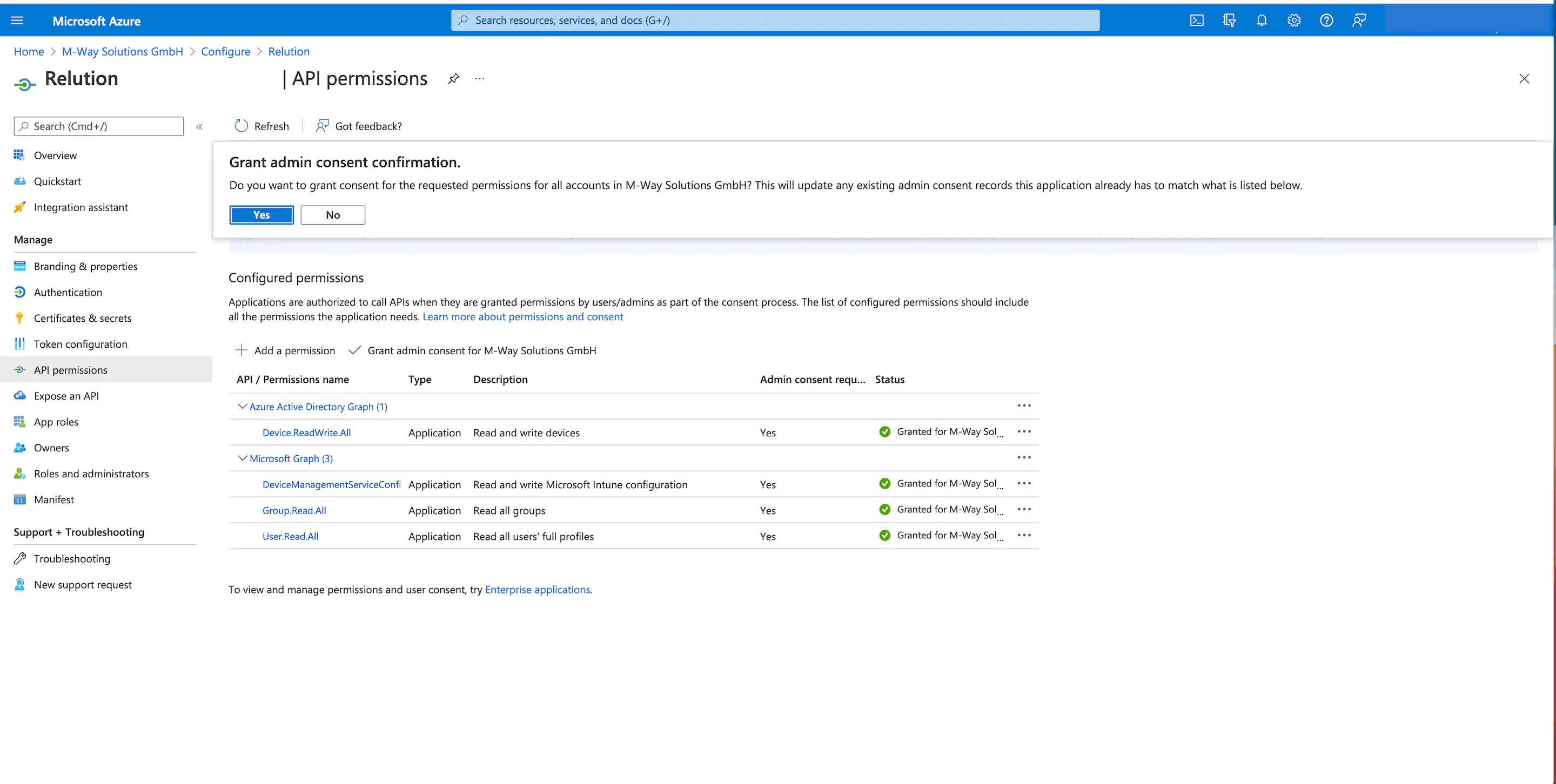
Configure API permissions
- Under
API Permissions > Configured Permissions, **Add Permission**should be clicked. - The
Microsoft Graphshould be selected underMicrosoft APIsin theRequest API Permissionsdialogue box.

- In the next step, the tile `Application permissions can be selected.
User.Read.Allfor can be selected forUser.

For the newly added API permissions, an exclamation mark is initially displayed as the status. Administrators must agree to this once in order for Microsoft Graph to ultimately receive the permissions. Afterwards, the status is displayed with a green check mark for
Grantedand the permissions are granted.
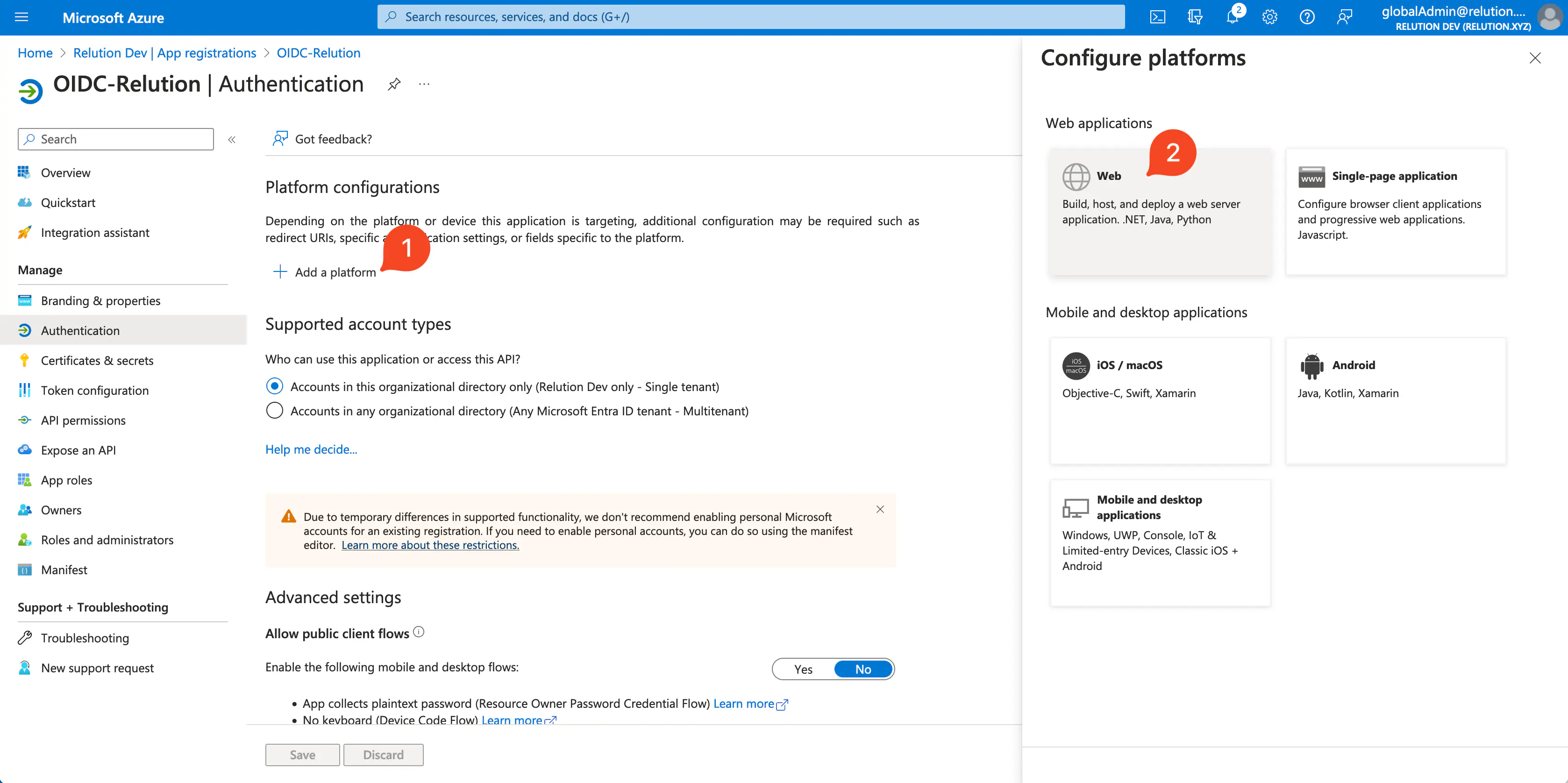
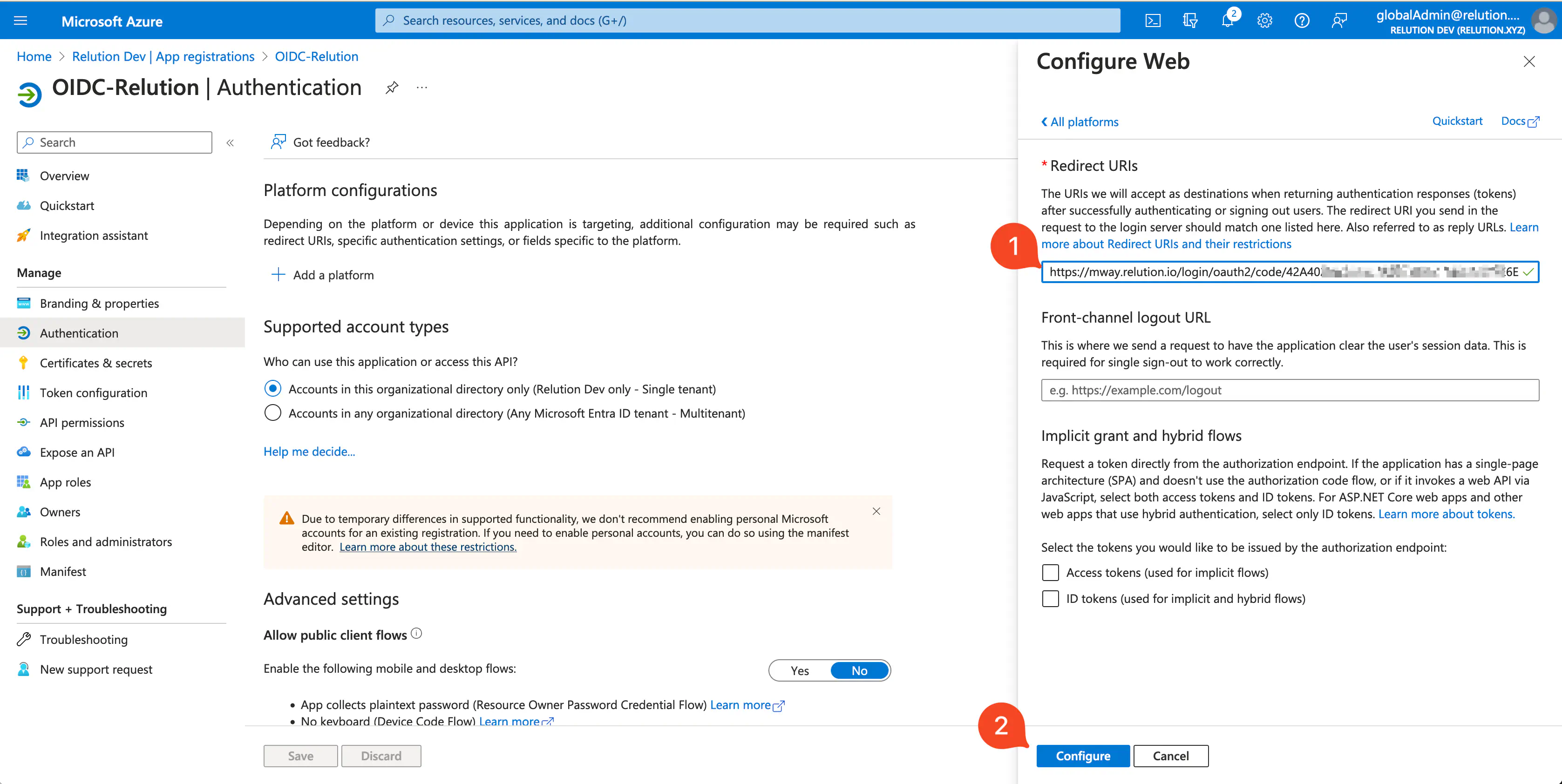
Add redirection URI
The redirection URI will be displayed in the Relution portal once the connection is configured and saved.
Additional Notes
Backchannel Logout
Backchannel Logout is supported in Relution starting with Server version 5.32.0.
ExempExample use case: A user is signed in to a central SSO service and multiple applications. When the user logs out of the SSO service, the backchannel logout ensures that all connected applications also terminate their sessions—even if running in the background.